Intrusion Testing (Pentest): the different types of tests
In one of our previous articles, we deconstructed what is a penetration test, also called an intrusion test. After having gone through and defined this method, it is now time to go deeper into the implementation of the pentest. This article aims to show you the different types of tests you can deploy during a penetration test.
A quick reminder of what a pentest is before getting to the heart of the matter
- The penetration test exists to map the security flaws of an information system, a web application, mobile application or software. The pentest detects vulnerabilities or possible attacks that have occurred on a system.
- The penetration test is much more concrete than a security audit for example. This is because it will provide a list of recommendations of actions to implement in order to improve the security of the IS.
- The pentest is also faster to implement than a security audit.
- Intrusion testing can be performed in two different ways: either directly internally, from the organization’s internal network, or externally via an Internet connection.
- The person who has the knowledge to perform a pentest is called a pentestor.
Let’s get even more practical and examine together the different types of penetration tests that are possible in the context of a pentest. We will then try to understand how to select the most appropriate type of test.
As previously mentioned, there are two types of penetration testing:
The external pentest
What is an external Pentest?
The person responsible for the test is called the slider or the attacker. It is a matter of testing the slater, by putting him in a situation. The latter will act as if he were a malicious hacker. He will try to get into the software, the application or the target information system. In this case, in order to perform this test, the public IP addresses of the pentester and the target are used.
What is an internal Pentest?
In the implementation of an internal pentest, the penetrator is present in the internal network of the company. Still in the position of an attacker, he will try to attack his target via the internal network directly. Indeed, this type of scenario can represent an attack coming from someone who is connected to the system, who is already inside the system (an employee for example or any person having access to the internal network).
In both cases of external and internal penetration testing, we analyze and study how the target will react and behave.
Indeed it is a point of attention that we must not forget and take into consideration. That is, whether voluntarily or not a person who has direct access to the internal network of a company, represents a risk:
- A spiteful or malicious employee.
- A contractor of any kind.
- A careless action from an employee who inserts an infected USB key on a computer or transmits a corrupted document, loses passwords and so on.
Under what conditions does the intrusion test take place?
Let’s go even deeper into the jargon used by the expert slater: the black box, the grey box and the white box. What is the purpose of these nicknames?
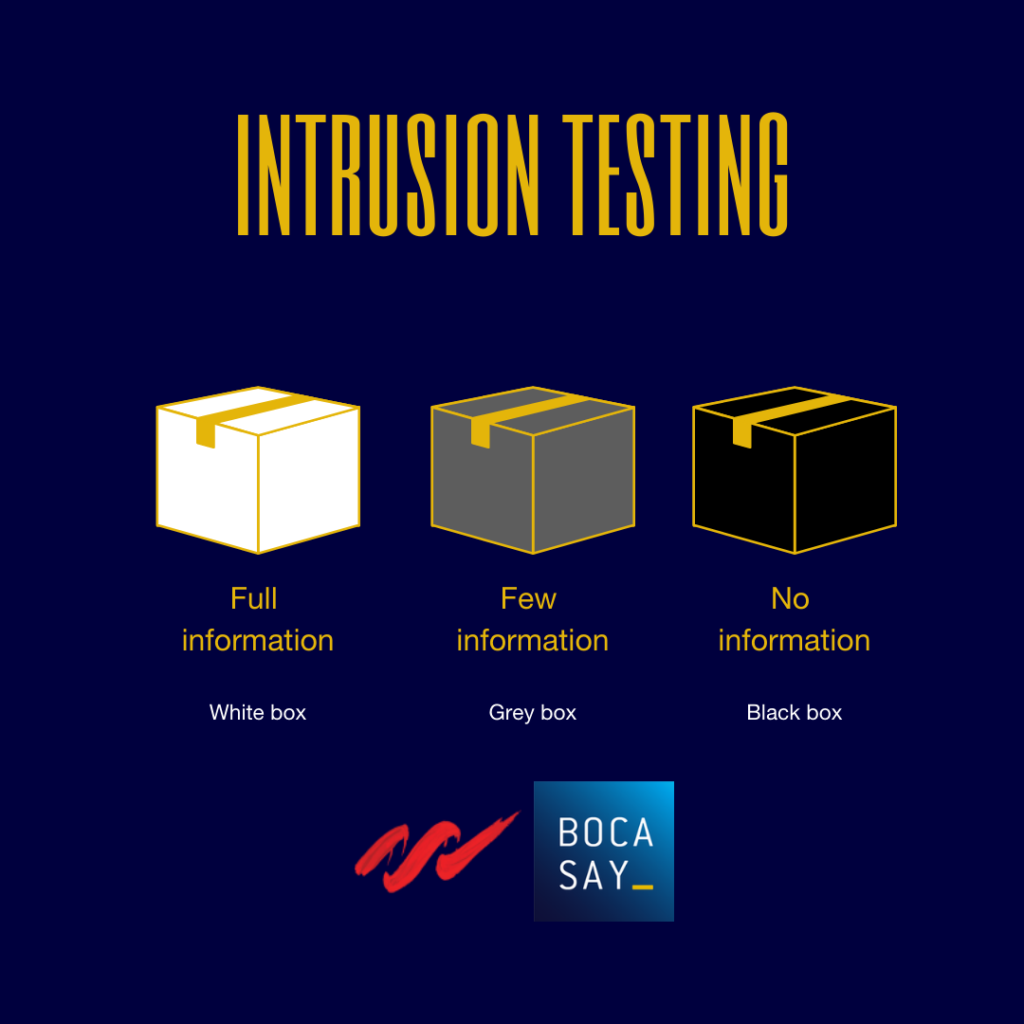
What is a black box in the context of a Pentest?
When the penetrator is in a black box situation, it means that he has no information about his target. He does not know anything about his target, neither passwords, nor identifiers etc.
In this type of scenario, the slater will start his work with an in-depth research of information about his target, such as, for example :
- General information about the company, its type, its field of activity, its history etc.
- The company’s employees, its partners.
- The geographical location of the company’s establishment(s).
In the case of the black box, the penetrator assumes the role of a hacker who breaks into an unfamiliar organization.
What is a gray box in the context of a Pentest?
The slater has very little information at the beginning of his test. Considering the scenario of a gray box can allow the slater to proceed faster and to focus his work on the analysis inside the system.
The slater can have a login and a password for example, which will help him to begin a concrete test quickly.
In this type of scenario, the slater has the role of an ordinary user who is already inside the target company.
What is a white box in the context of a Pentest?
Within the framework of a white box, the pentester behaves like an administrator of the system or networks of the organization. The pentester has a lot of information about the company, such as: documentation on the network architecture, user accounts to authenticate, software source code…
The white box confers the advantage of extracting, in the most complete and thorough way possible, all the flaws of the software or the IS.
How to choose between the black, grey or white box?
A black, gray or white box penetration test will not provide the same results and conclusions. The type of test, as well as the conditions of possession of the information from the start is very important. Make your choice according to the degree of risk you are facing. Indeed, ask yourself the question: what type of attack do you want to protect yourself from?
Example 1: You are a network manager in an online banking company. You are concerned about whether a hacker could steal the banking data you hold on your customers. In this case, go for a black box test, as the black box method is closest to the scenario you want to protect against.
Example 2: You are the head of an e-commerce company and you are in a serious conflict with one of your employees. You fear the worst, and are afraid that your employee will retaliate and launch an attack against your e-commerce site. In such a case, consider a grey box pentest so that the pentestor has access to the same data that your employee has.
Entrust your pentesting project to a team of experts who have an impressive know-how: Maltem Consulting Group will help you secure your applications.